Internet Technologies Tutorial
Internet refers to network of networks. In this network each computer is recognized by a globally unique address known as IP address. A special computer DNS (Domain Name Server) is used to give name to the IP Address so that user can locate a computer by a name.
For example,a DNS server will resolve a name http://www.tutorialspoint.com to a particular IP address to uniquely identify the computer on which this website is hosted.
Audience
This tutorial has been prepared for the students as well as professionals to ramp up quickly. This tutorial is also easily understood by general person with an interest in becoming computer literate.
Prerequisites
Before proceeding with this tutorial you should have a basic knowledge of Computers, which will help you in understanding this tutorial easily and quickly.
Internet Overview
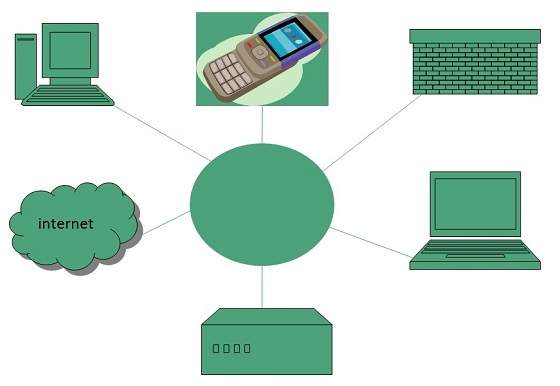
Internet
Internet is defined as an Information super Highway, to access information over the web. However, It can be defined in many ways as follows:
- Internet is a world-wide global system of interconnected computer networks.
- Internet uses the standard Internet Protocol (TCP/IP).
- Every computer in internet is identified by a unique IP address.
- IP Address is a unique set of numbers (such as 110.22.33.114) which identifies a computer location.
- A special computer DNS (Domain Name Server) is used to give name to the IP Address so that user can locate a computer by a name.
- For example, a DNS server will resolve a name http://www.tutorialspoint.com to a particular IP address to uniquely identify the computer on which this website is hosted.
- Internet is accessible to every user all over the world.
Evolution
The concept of Internet was originated in 1969 and has undergone several technological & Infrastructural changes as discussed below:
- The origin of Internet devised from the concept of Advanced Research Project Agency Network (ARPANET).
- ARPANET was developed by United States Department of Defense.
- Basic purpose of ARPANET was to provide communication among the various bodies of government.
- Initially, there were only four nodes, formally called Hosts.
- In 1972, the ARPANET spread over the globe with 23 nodes located at different countries and thus became known as Internet.
- By the time, with invention of new technologies such as TCP/IP protocols, DNS, WWW, browsers, scripting languages etc.,Internet provided a medium to publish and access information over the web.
Advantages
Internet covers almost every aspect of life, one can think of. Here, we will discuss some of the advantages of Internet:
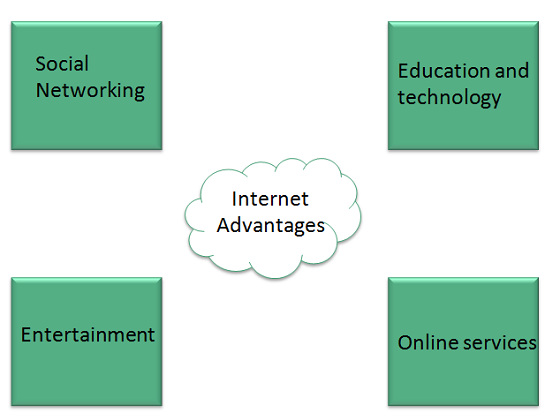
- Internet allows us to communicate with the people sitting at remote locations. There are various apps available on the wed that uses Internet as a medium for communication. One can find various social networking sites such as:
- Yahoo
- Google+
- Flickr
- Orkut
- One can surf for any kind of information over the internet. Information regarding various topics such as Technology, Health & Science, Social Studies, Geographical Information, Information Technology, Products etc can be surfed with help of a search engine.
- Apart from communication and source of information, internet also serves a medium for entertainment. Following are the various modes for entertainment over internet.
- Online Television
- Online Games
- Songs
- Videos
- Social Networking Apps
- Internet allows us to use many services like:
- Internet Banking
- Matrimonial Services
- Online Shopping
- Online Ticket Booking
- Online Bill Payment
- Data Sharing
- Internet provides concept of electronic commerce, that allows the business deals to be conducted on electronic systems
Disadvantages
However, Internet has prooved to be a powerful source of information in almost every field, yet there exists many disadvanatges discussed below:
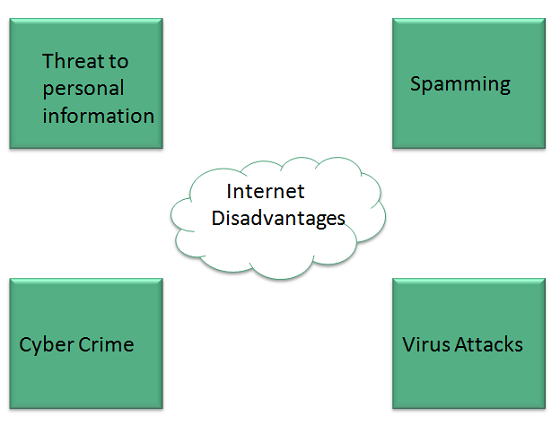
- There are always chances to loose personal information such as name, address, credit card number. Therefore, one should be very careful while sharing such information. One should use credit cards only through authenticated sites.
- Another disadvantage is the Spamming.Spamming corresponds to the unwanted e-mails in bulk. These e-mails serve no purpose and lead to obstruction of entire system.
- Virus can easily be spread to the computers connected to internet. Such virus attacks may cause your system to crash or your important data may get deleted.
- Also a biggest threat on internet is pornography. There are many pornographic sites that can be found, letting your children to use internet which indirectly affects the children healthy mental life.
- There are various websites that do not provide the authenticated information. This leads to misconception among many people.
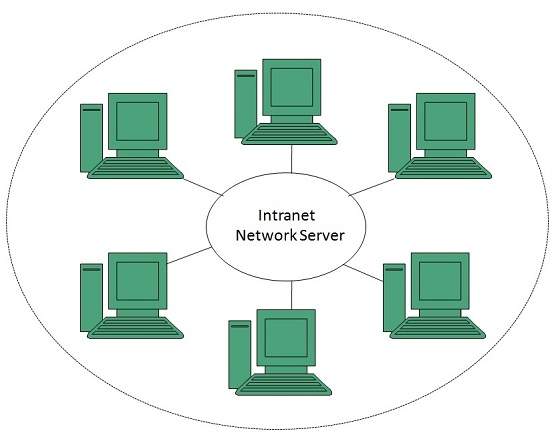
Intranet Overview
Intranet
Intranet is defined as private network of computers within an organization with its own server and firewall. Moreover we can define Intranet as:- Intranet is system in which multiple PCs are networked to be connected to each other. PCs in intranet are not available to the world outside of the intranet.
- Usually each company or organization has their own Intranet network and members/employees of that company can access the computers in their intranet.
- Every computer in internet is identified by a unique IP address.
- Each computer in Intranet is also identified by a IP Address, which is unique among the computers in that Intranet.
Benefits
Intranet is very efficient and reliable network system for any organization. It is beneficial in every aspect such as collaboration, cost-effectiveness, security, productivity and much more.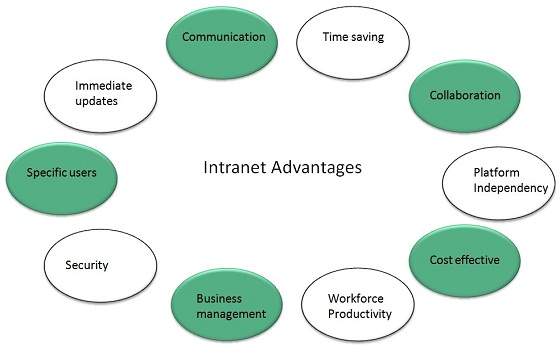
Communication
Intranet offers easy and cheap communication within an organization. Employees can communicate using chat, e-mail or blogs.Time Saving
Information on Intranet is shared in real time.Collaboration
Information is distributed among the employees as according to requirement and it can be accessed by the authorized users, resulting in enhanced teamwork.Platform Independency
Intranet can connect computers and other devices with different architecture.Cost Effective
Employees can see the data and other documents using browser rather than printing them and distributing duplicate copies among the employees, which certainly decreases the cost.Workforce Productivity
Data is available at every time and can be accessed using company workstation. This helps the employees work faster.Business Management
It is also possible to deploy applications that support business operations.Security
Since information shared on intranet can only be accessed within an organization, therefore there is almost no chance of being theft.Specific Users
Intranet targets only specific users within an organization therefore, once can exactly know whom he is interacting.Immediate Updates
Any changes made to information are reflected immediately to all the users.Issues
Apart from several benefits of Intranet, there also exist some issues.. These issues are shown in the following diagram: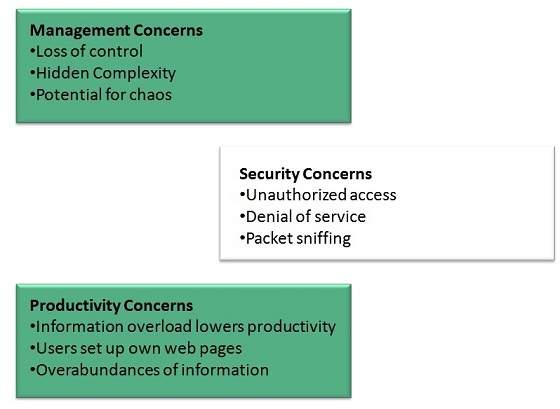
Applications
Intranet applications are same as that of Internet applications. Intranet applications are also accessed through a web browser. The only difference is that, Intranet applications reside on local server while Internet applications reside on remote server. Here, we've discussed some of these applications: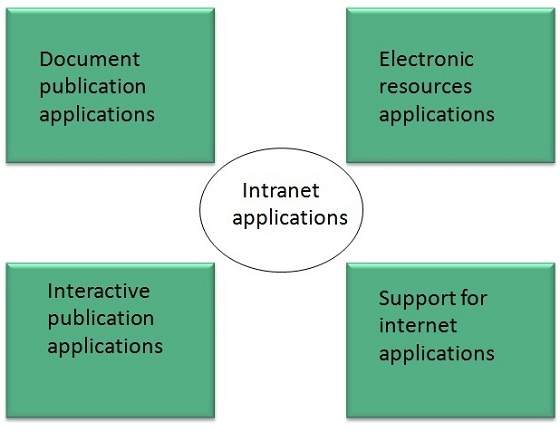
Document publication applications
Document publication applications allow publishing documents such as manuals, software guide, employee profits etc without use of paper.Electronic resources applications
It offers electronic resources such as software applications, templates and tools, to be shared across the network.Interactive Communication applications
Like on internet, we have e-mail and chat like applications for Intranet, hence offering an interactive communication among employees.Support for Internet Applications
Intranet offers an environment to deploy and test applications before placing them on Internet.Internet vs. Intranet
Apart from similarities there are some differences between the two. Following are the differences between Internet and Intranet:IntranetInternetLocalized Network.Worldwide NetworkDoesn't have access to IntranetHave access to Internet.More ExpensiveLess ExpensiveMore SafeLess SafeMore ReliabilityLess ReliabilityExtranet Overview
Extranet
Extranet refers to network within an organization, using internet to connect to the outsiders in controlled manner. It helps to connect businesses with their customers and suppliers and therefore allows working in a collaborative manner.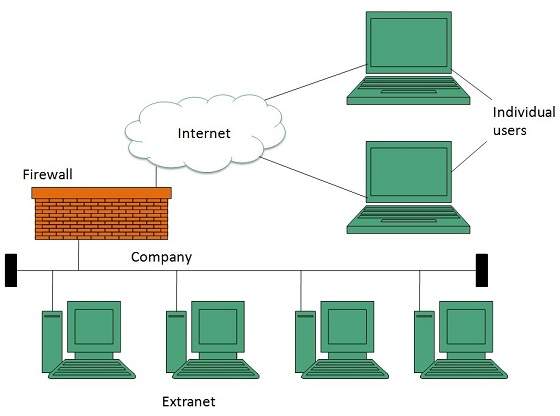
Implementation
Extranet is implemented as a Virtual Private Networks (VPN) because it uses internet to connect to corporate organization and there is always a threat to information security. VPN offers a secure network in public infrastructure (Internet).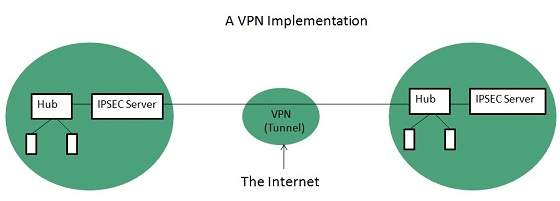
Key Points- The packet is encapsulated at boundary of networks in IPSEC complaint routers.
- It uses an encryption key to encapsulate packets and IP addresses as well.
- The packet is decoded only by the IPSEC complaint routers or servers.
- The message is sent over VPN via VPN Tunnel and this process is known as tunneling.
VPN uses Internet Protocol Security Architecture (IPSEC) Protocol to provide secure transactions by adding an additional security layer to TCP/IP protocol. This layer is created by encapsulating the IP packet to a new IP packet as shown in the following diagram: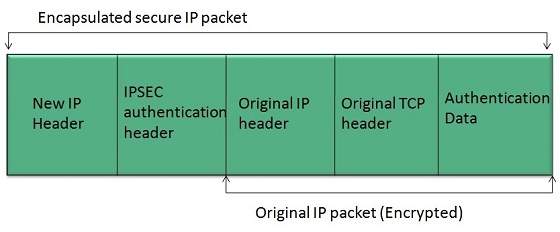
Benefits
Extranet proves to be a successful model for all kind of businesses whether small or big. Here are some of the advantages of extranet for employees, suppliers, business partners, and customers: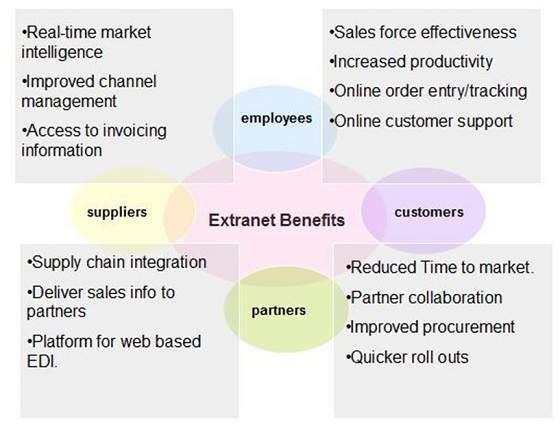
Issues
Apart for advantages there are also some issues associated with extranet. These issues are discussed below:Hosting
Where the extranet pages will be held i.e. who will host the extranet pages. In this context there are two choices:- Host it on your own server.
- Host it with an Internet Service Provider (ISP) in the same way as web pages.
But hosting extranet pages on your own server requires high bandwidth internet connection which is very costly.Security
Additional firewall security is required if you host extranet pages on your own server which result in a complex security mechanism and increase work load.Accessing Issues
Information can not be accessed without internet connection. However, information can be accessed in Intranet without internet connection.Decreased Interaction
It decreases the face to face interaction in the business which results in lack of communication among customers, business partners and suppliers.Extranet vs. Intranet
The following table shows differences between Extranet and Intranet:- ExtranetIntranetInternal network that can be accessed externally.Internal network that can not be accessed externally.Extranet is extension of company's Intranet.Only limited users of a company.For limited external communication between customers, suppliers and business partners.Only for communication within a company.
Internet Reference Models
Reference Model
Reference Model offers a means of standardization which is acceptable worldwide. Since people using the computer network are located over a wide physical range and their network devices might have heterogeneous architecture. In order to provide communication among heterogeneous devices, we need a standardized model i.e. a reference model, which would provide us way how these devices can communicate regardless their architecture.We have two reference models such as OSI model and TCP/IP reference model, however, the OSI model is a hypothetical one but the TCP/IP is absolutely practical model.OSI Model
OSI is acronym of Open System Interface. This model is developed by the International organization of Standardization (ISO) and therefore also referred as ISO-OSI Model.The OSI model consists of seven layers as shown in the following diagram. Each layer has a specific function, however each layer provide services to the layer above.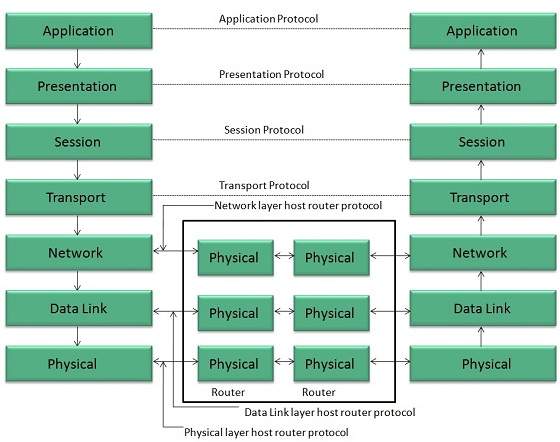
Physical Layer
The Physical layer is responsible for the following activities:- Activating, maintaining and deactivating the physical connection.
- Defining voltages and data rates needed for transmission.
- Converting digital bits into electrical signal.
- Deciding whether the connection is simplex, half duplex or full duplex.
- Performs synchronization and error control for the information which is to be transmitted over the physical link.
- Enables error detection, and adds error detection bits to the data which are to be transmitted.
- To route the signals through various channels to the other end.
- To act as the network controller by deciding which route data should take.
- To divide the outgoing messages into packets and to assemble incoming packets into messages for higher levels.
- It decides if the data transmission should take place on parallel paths or single path.
- It performs multiplexing, splitting on the data.
- It breaks the data groups into smaller units so that they are handled more efficiently by the network layer.
- Manages the messages and synchronizes conversations between two different applications.
- It controls logging on and off, user identification, billing and session management.
- This layer makes it sure that the information is delivered in such a form that the receiving system will understand and use it.
- It provides different services such as manipulation of information in several ways, retransferring the files of information, distributing the results etc.
- The functions such as LOGIN or password checking are also performed by the application layer.
- It provides different services such as manipulation of information in several ways, retransferring the files of information, distributing the results etc.
- The functions such as LOGIN or password checking are also performed by the application layer.
- It uses TCP and UDP protocol for end to end transmission.
- TCP is reliable and connection oriented protocol.
- TCP also handles flow control.
- The UDP is not reliable and a connection less protocol also does not perform flow control.
Data Link Layer
The data link layer performs the following functions:
Network Layer
Following are the functions of Network Layer:
Transport Layer
The Transport layer performs the following functions:
The Transport Layer guarantees transmission of data from one end to other end.
Session Layer
The Session layer performs the following functions:
Presentation Layer
The Presentation layer performs the following functions:
Application Layer
The Application layer performs the following functions:
TCP/IP Model
TCP/IP model is practical model and is used in the Internet. TCP/IP is acronym of Transmission Control Protocol and Internet Protocol.
The TCP/IP model combines the two layers (Physical and Data link layer) into one layer i.e. Host-to-Network layer. The following diagram shows the various layers of TCP/IP model:
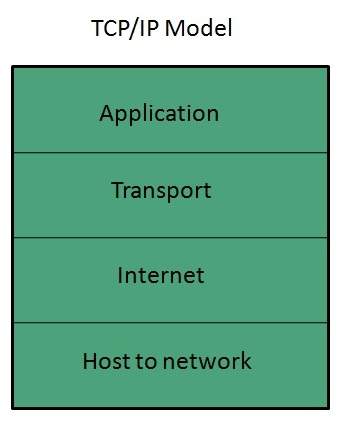
Application Layer
This layer is same as that of the OSI model and performs the following functions:
Protocols used: TELNET, FTP, SMTP, DN, HTTP, NNTP are the protocols employed in this layer.
Transport Layer
It does the same functions as that of transport layer in OSI model. Here are the key points regarding transport layer:
Protocols used: TCP/IP and UDP protocols are employed in this layer.
Internet Layer
The function of this layer is to allow the host to insert packets into network and then make them travel independently to the destination. However, the order of receiving the packet can be different from the sequence they were sent.
Protocols used: Internet Protocol (IP) is employed in Internet layer.
Host-to-Network Layer
This is the lowest layer in TCP/IP model. The host has to connect to network using some protocol, so that it can send IP packets over it. This protocol varies from host to host and network to network.
Protocols used: ARPANET, SATNET, LAN, packet radio are the protocols which are used in this layer.
Internet Domain Name System
Overview
When DNS was not into existence, one had to download a Host filecontaining host names and their corresponding IP address. But with increase in number of hosts of internet, the size of host file also increased. This resulted in increased traffic on downloading this file. To solve this problem the DNS system was introduced.
Domain Name System helps to resolve the host name to an address. It uses a hierarchical naming scheme and distributed database of IP addresses and associated names
IP Address
IP address is a unique logical address assigned to a machine over the network. An IP address exhibits the following properties:
- IP address is the unique address assigned to each host present on Internet.
- IP address is 32 bits (4 bytes) long.
- IP address consists of two components: network component and host component.
- Each of the 4 bytes is represented by a number from 0 to 255, separated with dots. For example 137.170.4.124
IP address is 32-bit number while on the other hand domain names are easy to remember names. For example, when we enter an email address we always enter a symbolic string such as webmaster@tutorialspoint.com.
Uniform Resource Locator (URL)
Uniform Resource Locator (URL) refers to a web address which uniquely identifies a document over the internet.
This document can be a web page, image, audio, video or anything else present on the web.
For example, www.tutorialspoint.com/internet_technology/index.htmlis an URL to the index.html which is stored on tutorialspoint web server under internet_technology directory.
URL Types
There are two forms of URL as listed below:
- Absolute URL
- Relative URL
ABSOLUTE URL
Absolute URL is a complete address of a resource on the web. This completed address comprises of protocol used, server name, path name and file name.
For example http:// www.tutorialspoint.com / internet_technology /index.htm. where:
- http is the protocol.
- tutorialspoint.com is the server name.
- index.htm is the file name.
The protocol part tells the web browser how to handle the file. Similarly we have some other protocols also that can be used to create URL are:
- FTP
- https
- Gopher
- mailto
- news
RELATIVE URL
Relative URL is a partial address of a webpage. Unlike absolute URL, the protocol and server part are omitted from relative URL.
Relative URLs are used for internal links i.e. to create links to file that are part of same website as the WebPages on which you are placing the link.
For example, to link an image on tutorialspoint.com/internet_technology/internet_referemce_models, we can use the relative URL which can take the form like /internet_technologies/internet-osi_model.jpg.
Difference between Absolute and Relative URL
Absolute URL
Relative URL
Used to link web pages on different websites
Used to link web pages within the same website.
Difficult to manage.
Easy to Manage
Changes when the server name or directory name changes
Remains same even of we change the server name or directory name.
Take time to access
Comparatively faster to access.
:Domain Name System Architecture
Absolute URL
Relative URL
Used to link web pages on different websites
Used to link web pages within the same website.
Difficult to manage.
Easy to Manage
Changes when the server name or directory name changes
Remains same even of we change the server name or directory name.
Take time to access
Comparatively faster to access.
The Domain name system comprises of Domain Names, Domain Name Space, Name Server that have been described below
Domain Names
Domain Name is a symbolic string associated with an IP address. There are several domain names available; some of them are generic such as com, edu, gov, net etc, while some country level domain names such as au, in, za, usetc.
The following table shows the Generic Top-Level Domain names:
Domain Name
|
Meaning
|
Com
|
Commercial business
|
Edu
|
Education
|
Gov
|
U.S. government agency
|
Int
|
International entity
|
Mil
|
U.S. military
|
Net
|
Networking organization
|
Org
|
Non profit organization
|
Domain Name
|
Meaning
|
au
|
Australia
|
in
|
India
|
cl
|
Chile
|
fr
|
France
|
us
|
United States
|
za
|
South Africa
|
uk
|
United Kingdom
|
jp
|
Japan
|
es
|
Spain
|
de
|
Germany
|
ca
|
Canada
|
ee
|
Estonia
|
hk
|
Hong Kong
|
Domain Name Space
The domain name space refers a hierarchy in the internet naming structure. This hierarchy has multiple levels (from 0 to 127), with a root at the top. The following diagram shows the domain name space hierarchy:
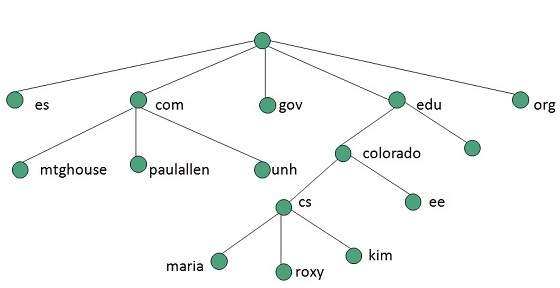
In the above diagram each subtree represents a domain. Each domain can be partitioned into sub domains and these can be further partitioned and so on.
Name Server
Name server contains the DNS database. This database comprises of various names and their corresponding IP addresses. Since it is not possible for a single server to maintain entire DNS database, therefore, the information is distributed among many DNS servers.
Zones
Zone is collection of nodes (sub domains) under the main domain. The server maintains a database called zone file for every zone.
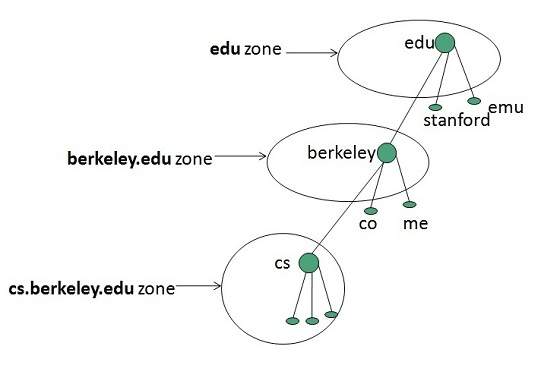
If the domain is not further divided into sub domains then domain and zone refers to the same thing.
The information about the nodes in the sub domain is stored in the servers at the lower levels however; the original server keeps reference to these lower levels of servers.
TYPES OF NAME SERVERS
Following are the three categories of Name Servers that manages the entire Domain Name System:
- Root Server
- Primary Server
- Secondary Server
ROOT SERVER
Root Server is the top level server which consists of the entire DNS tree. It does not contain the information about domains but delegates the authority to the other server
PRIMARY SERVERS
Primary Server stores a file about its zone. It has authority to create, maintain, and update the zone file.
SECONDARY SERVER
Secondary Server transfers complete information about a zone from another server which may be primary or secondary server. The secondary server does not have authority to create or update a zone file.
DNS Working
DNS translates the domain name into IP address automatically. Following steps will take you through the steps included in domain resolution process:
- When we type www.tutorialspoint.com into the browser, it asks the local DNS Server for its IP address.
- When the local DNS does not find the IP address of requested domain name, it forwards the request to the root DNS server and again enquires about IP address of it.
- The root DNS server replies with delegation that I do not know the IP address of www.tutorialspoint.com but know the IP address of DNS Server.
- The local DNS server then asks the com DNS Server the same question.
- The com DNS Server replies the same that it does not know the IP address of www.tutorialspont.com but knows the address of tutorialspoint.com.
- Then the local DNS asks the tutorialspoint.com DNS server the same question.
- Then tutorialspoint.com DNS server replies with IP address of www.tutorialspoint.com.
- Now, the local DNS sends the IP address of www.tutorialspoint.com to the computer that sends the request.
Here the local DNS is at ISP end.
Internet Services
Internet Services allows us to access huge amount of information such as text, graphics, sound and software over the internet. Following diagram shows the four different categories of Internet Services.
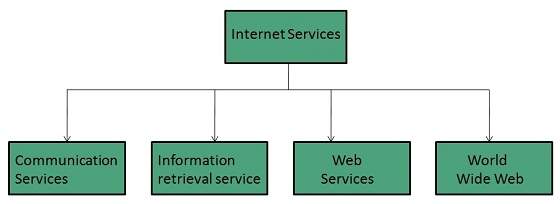
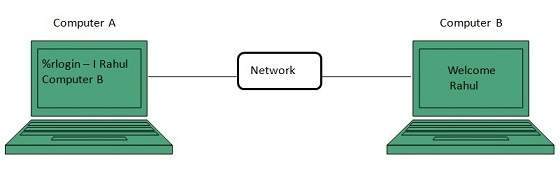
Communication Services
There are various Communication Services available that offer exchange of information with individuals or groups. The following table gives a brief introduction to these services:
S.N.
|
Service Description
|
1
|
Electronic Mail
Used to send electronic message over
the internet.
|
2
|
Telnet
Used to log on to a remote computer
that is attached to internet.
|
3
|
Newsgroup
Offers a forum for people to discuss
topics of common interests.
|
4
|
Internet Relay Chat (IRC)
Allows the people from all over the
world to communicate in real time.
|
5
|
Mailing Lists
Used to organize group of internet
users to share common information through e-mail.
|
6
|
Internet Telephony (VoIP)
Allows the internet users to talk
across internet to any PC equipped to receive the call.
|
7
|
Instant Messaging
Offers real time chat between
individuals and group of people. Eg. Yahoo messenger, MSN messenger.
|
There exist several Information retrieval services offering easy access to information present on the internet. The following table gives a brief introduction to these services:Information Retrieval Services
S.N.
|
Service Description
|
1
|
File Transfer Protocol (FTP)
Enable the users to transfer files.
|
2
|
Archie
It’s updated database of public FTP
sites and their content. It helps to search a file by its name.
|
3
|
Gopher
Used to search, retrieve, and display
documents on remote sites.
|
4
|
Very Easy Rodent Oriented Netwide
Index to Computer Achieved (VERONICA)
VERONICA is gopher based resource. It
allows access to the information resource stored on gopher’s servers.
|
Web services allow exchange of information between applications on the web. Using web services, applications can easily interact with each other.Web Services
The web services are offered using concept of Utility Computing.
World Wide Web (WWW)
WWW is also known as W3. It offers a way to access documents spread over the several servers over the internet. These documents may contain texts, graphics, audio, video, hyperlinks. The hyperlinks allow the users to navigate between the documents.
Video Conferencing
Video conferencing or Video teleconferencing is a method of communicating by two-way video and audio transmission with help of telecommunication technologies.
Modes of Video Conferencing
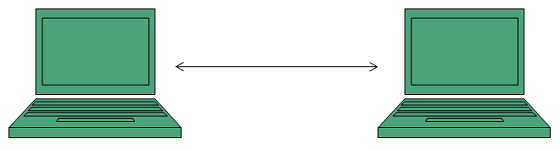
POINT-TO-POINT
This mode of conferencing connects two locations only.
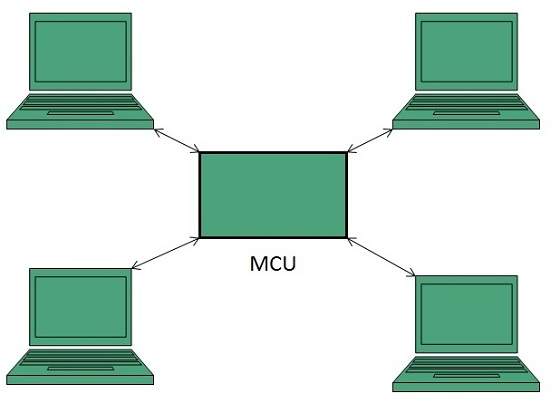
MULTI-POINT
This mode of conferencing connects more than two locations through Multi-point Control Unit (MCU).
Internet Connectivity
Internet Service Providers (ISP)
Internet Service Provider (ISP) is a company offering access to internet. They offer various services:
- Internet Access
- Domain name registration
- Dial-up access
- Leased line access
ISP Types
ISPs can broadly be classified into six categories as shown in the following diagram:
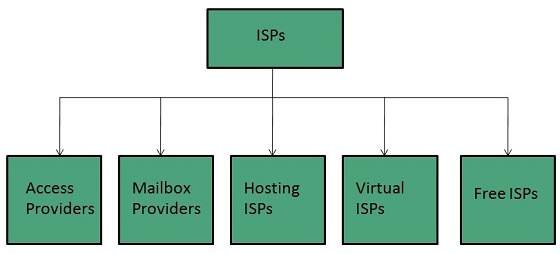
ACCESS PROVIDERS
They provide access to internet through telephone lines, cable wi-fi or fiber optics.
MAILBOX PROVIDER
Such providers offer mailbox hosting services.
HOSTING ISPS
Hosting ISPs offers e-mail, and other web hosting services such as virtual machines, clouds etc.
VIRTUAL ISPS
Such ISPs offer internet access via other ISP services.
FREE ISPS
Free ISPs do not charge for internet services.
Connection Types
There exist several ways to connect to the internet. Following are these connection types available:
- Dial-up Connection
- ISDN
- DSL
- Cable TV Internet connections
- Satellite Internet connections
- Wireless Internet Connections
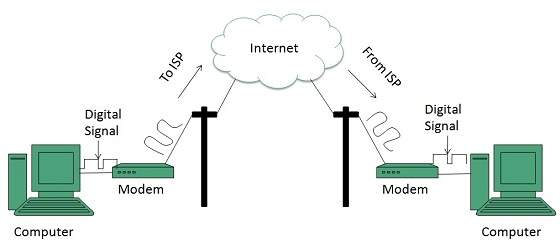
Dial-up Connection
Dial-up connection uses telephone line to connect PC to the internet. It requires a modem to setup dial-up connection. This modem works as an interface between PC and the telephone line.
There is also a communication program that instructs the modem to make a call to specific number provided by an ISP.
Dial-up connection uses either of the following protocols:
- Serial Line Internet Protocol (SLIP)
- Point to Point Protocol (PPP)
The following diagram shows the accessing internet using modem:
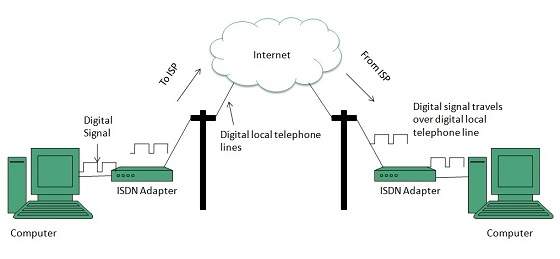
ISDN
ISDN is acronym of Integrated Services Digital Network. It establishes the connection using the phone lines which carry digital signals instead of analog signals.
There are two techniques to deliver ISDN services:
- Basic Rate Interface (BRI)
- Primary Rate Interface (PRI)
Key points:
- The BRI ISDN consists of three distinct channels on a single ISDN line: t1o 64kbps B (Bearer) channel and one 16kbps D (Delta or Data) channels.
- The PRI ISDN consists of 23 B channels and one D channels with both have operating capacity of 64kbps individually making a total transmission rate of 1.54Mbps.
The following diagram shows accessing internet using ISDN connection:
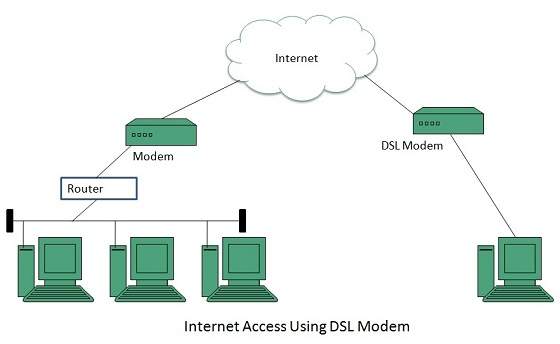
DSL
DSL is acronym of Digital Subscriber Line. It is a form of broadband connection as it provides connection over ordinary telephone lines.
Following are the several versions of DSL technique available today:
- Asymmetric DSL (ADSL)
- Symmetric DSL (SDSL)
- High bit-rate DSL (HDSL)
- Rate adaptive DSL (RDSL)
- Very high bit-rate DSL (VDSL)
- ISDN DSL (IDSL)
All of the above mentioned technologies differ in their upload and download speed, bit transfer rate and level of service.
The following diagram shows that how we can connect to internet using DSL technology:
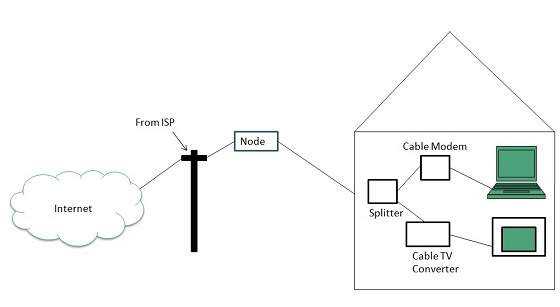
Cable TV Internet Connection
Cable TV Internet connection is provided through Cable TV lines. It uses coaxial cable which is capable of transferring data at much higher speed than common telephone line.
Key Points:
- A cable modem is used to access this service, provided by the cable operator.
- The Cable modem comprises of two connections: one for internet service and other for Cable TV signals.
- Since Cable TV internet connections share a set amount of bandwidth with a group of customers, therefore, data transfer rate also depends on number of customers using the internet at the same time.
The following diagram shows that how internet is accessed using Cable TV connection:
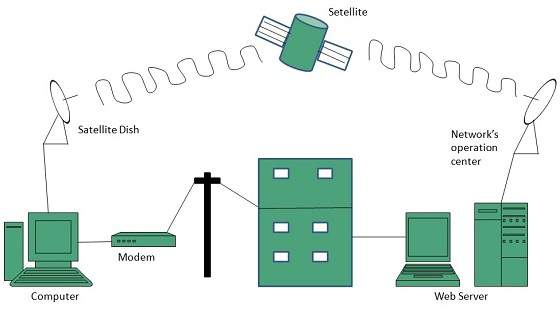
Satellite Internet Connection
Satellite Internet connection offers high speed connection to the internet. There are two types of satellite internet connection: one way connection or two way connection.
In one way connection, we can only download data but if we want to upload, we need a dialup access through ISP over telephone line.
In two way connection, we can download and upload the data by the satellite. It does not require any dialup connection.
The following diagram shows how internet is accessed using satellite internet connection:
Wireless Internet Connection
Wireless Internet Connection makes use of radio frequency bands to connect to the internet and offers a very high speed. The wireless internet connection can be obtained by either WiFi or Bluetooth.
Key Points:
- Wi Fi wireless technology is based on IEEE 802.11 standards which allow the electronic device to connect to the internet.
- Bluetooth wireless technology makes use of short-wavelength radio waves and helps to create personal area network (PAN).
Internet Protocols
Transmission Control Protocol (TCP)
TCP is a connection oriented protocol and offers end-to-end packet delivery. It acts as back bone for connection.It exhibits the following key features:
- Transmission Control Protocol (TCP) corresponds to the Transport Layer of OSI Model.
- TCP is a reliable and connection oriented protocol.
- TCP offers:
- Stream Data Transfer.
- Reliability.
- Efficient Flow Control
- Full-duplex operation.
- Multiplexing.
- TCP offers connection oriented end-to-end packet delivery.
- TCP ensures reliability by sequencing bytes with a forwarding acknowledgement number that indicates to the destination the next byte the source expect to receive.
- It retransmits the bytes not acknowledged with in specified time period.
TCP Services
TCP offers following services to the processes at the application layer:
- Stream Delivery Service
- Sending and Receiving Buffers
- Bytes and Segments
- Full Duplex Service
- Connection Oriented Service
- Reliable Service
STREAM DELIVER SERVICE
TCP protocol is stream oriented because it allows the sending process to send data as stream of bytes and the receiving process to obtain data as stream of bytes.
SENDING AND RECEIVING BUFFERS
It may not be possible for sending and receiving process to produce and obtain data at same speed, therefore, TCP needs buffers for storage at sending and receiving ends.
BYTES AND SEGMENTS
The Transmission Control Protocol (TCP), at transport layer groups the bytes into a packet. This packet is called segment. Before transmission of these packets, these segments are encapsulated into an IP datagram.
FULL DUPLEX SERVICE
Transmitting the data in duplex mode means flow of data in both the directions at the same time.
CONNECTION ORIENTED SERVICE
TCP offers connection oriented service in the following manner:
- TCP of process-1 informs TCP of process – 2 and gets its approval.
- TCP of process – 1 and TCP of process – 2 and exchange data in both the two directions.
- After completing the data exchange, when buffers on both sides are empty, the two TCP’s destroy their buffers.
RELIABLE SERVICE
For sake of reliability, TCP uses acknowledgement mechanism.
Internet Protocol (IP)
Internet Protocol is connectionless and unreliable protocol. It ensures no guarantee of successfully transmission of data.
In order to make it reliable, it must be paired with reliable protocol such as TCP at the transport layer.
Internet protocol transmits the data in form of a datagram as shown in the following diagram:
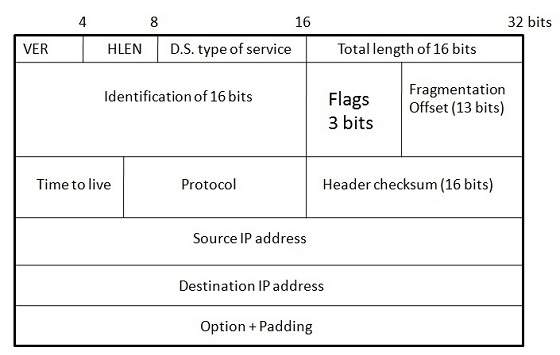
Points to remember:
- The length of datagram is variable.
- The Datagram is divided into two parts: header and data.
- The length of header is 20 to 60 bytes.
- The header contains information for routing and delivery of the packet.
User Datagram Protocol (UDP)
Like IP, UDP is connectionless and unreliable protocol. It doesn’t require making a connection with the host to exchange data. Since UDP is unreliable protocol, there is no mechanism for ensuring that data sent is received.
UDP transmits the data in form of a datagram. The UDP datagram consists of five parts as shown in the following diagram:
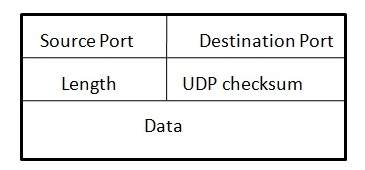
Points to remember:
- UDP is used by the application that typically transmit small amount of data at one time.
- UDP provides protocol port used i.e. UDP message contains both source and destination port number, that makes it possible for UDP software at the destination to deliver the message to correct application program.
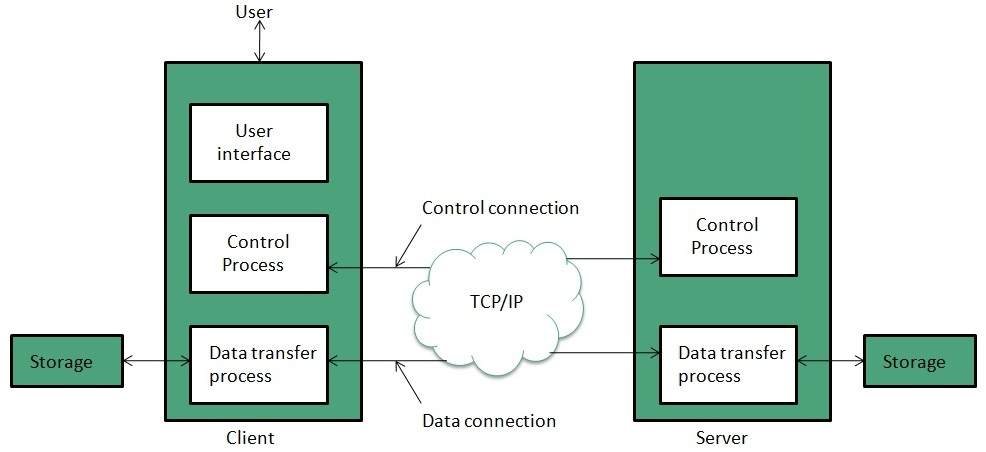
File Transfer Protocol (FTP)
FTP is used to copy files from one host to another. FTP offers the mechanism for the same in following manner:
- FTP creates two processes such as Control Process and Data Transfer Process at both ends i.e. at client as well as at server.
- FTP establishes two different connections: one is for data transfer and other is for control information.
- Control connection is made between control processes while Data Connection is made between
- FTP uses port 21 for the control connection and Port 20 for the data connection.
Trivial File Transfer Protocol (TFTP)
Trivial File Transfer Protocol is also used to transfer the files but it transfers the files without authentication. Unlike FTP, TFTP does not separate control and data information. Since there is no authentication exists, TFTP lacks in security features therefore it is not recommended to use TFTP.
Key points
- TFTP makes use of UDP for data transport. Each TFTP message is carried in separate UDP datagram.
- The first two bytes of a TFTP message specify the type of message.
- The TFTP session is initiated when a TFTP client sends a request to upload or download a file.
- The request is sent from an ephemeral UDP port to the UDP port 69 of an TFTP server.
Difference between FTP and TFTP
S.N.
|
Parameter
|
FTP
|
TFTP
|
1
|
Operation
|
Transferring Files
|
Transferring Files
|
2
|
Authentication
|
Yes
|
No
|
3
|
Protocol
|
TCP
|
UDP
|
4
|
Ports
|
21 – Control, 20 – Data
|
Port 3214, 69, 4012
|
5
|
Control and Data
|
Separated
|
Separated
|
6
|
Data Transfer
|
Reliable
|
Unreliable
|
Hyper Text Transfer Protocol (HTTP)
HTTP is a communication protocol. It defines mechanism for communication between browser and the web server. It is also called request and response protocol because the communication between browser and server takes place in request and response pairs.
HTTP Request
HTTP request comprises of lines which contains:
- Request line
- Header Fields
- Message body
Key Points
- The first line i.e. the Request line specifies the request method i.e. Get or Post.
- The second line specifies the header which indicates the domain name of the server from where index.htm is retrieved.
HTTP Response
Like HTTP request, HTTP response also has certain structure. HTTP response contains:
- Status line
- Headers
- Message body


0 comments:
Post a Comment